Background
ACME, a leading financial sector company with multiple lines of business, has implemented a stringent security review program that mandates each application or implementation undergo a thorough security evaluation before being approved for production or go-live. This program is not just a compliance requirement but a critical measure to ensure the security and integrity of the firm’s diverse financial services, which cater to a vast and varied clientele. By maintaining this high standard, ACME continues to uphold its reputation as a secure and reliable financial institution.
Challenge
ACME operates in an extremely fast-paced development environment characterized by various development models, including custom-developed applications, third-party platforms for in-house apps, vendor applications with Single Sign-On (SSO) implementations, and frequent sprint releases. Each development type brings unique security challenges that require a tailored approach to testing, ensuring that all potential risks are addressed. Moreover, the complexity of coordinating between separate teams, managing pre-requisites, and ensuring the integrity of data across multiple departments further complicates the security review process. The need for seamless communication, precise planning, and the alignment of multiple stakeholders adds layers of difficulty in ensuring that security assessments are both comprehensive and timely.
Solution
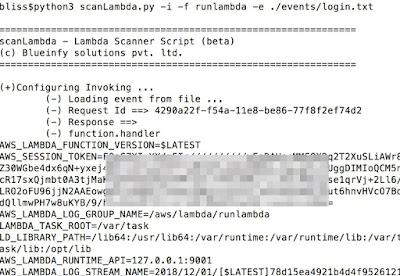
To address these multifaceted challenges, ACME partnered with Blueinfy, entrusting them with the complete management of the security testing process from start to finish:
Pre-Requisites Sharing and Access Verification:
Blueinfy begins each engagement by ensuring that all necessary pre-requisites are thoroughly shared, and access to relevant systems is meticulously verified before any testing commences. This careful preparation is crucial for setting up a test environment that accurately mirrors the production environment, thereby ensuring that security assessments are realistic and reliable. By verifying access and prerequisites early, Blueinfy minimizes the risk of encountering delays or oversights during testing.
Scheduling Demos to Understand Applications/Implementations:
Before diving into the technical aspects of testing, Blueinfy schedules detailed demonstrations with ACME’s internal teams to gain a deep understanding of each application or implementation. These sessions are designed to uncover any unique functionalities, workflows, or potential vulnerabilities that might not be immediately apparent. This proactive approach ensures that the subsequent security testing is not just a box-checking exercise but a thorough examination tailored to the specific nuances of the application, increasing the likelihood of identifying any subtle or context-specific risks.
Scoping/Test Scenario Preparation:
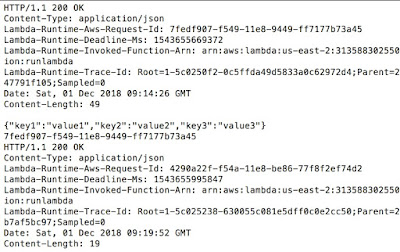
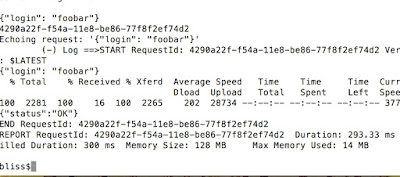
Based on the understanding gained from these demos, Blueinfy meticulously narrows down the scope of the penetration test according to the nature of the changes being implemented. Whether it’s a full-blown penetration test, a limited scope assessment for specific enhancements, a client-side mobile application, API penetration test, or SSO implementation, the scope is carefully defined to match the specific needs of the project. This targeted approach not only ensures that the testing is highly relevant but also enables faster report delivery and more efficient budget utilization, aligning with ACME’s need for both speed and precision in their fast-paced environment.Thorough Penetration Testing:
Blueinfy’s penetration testing is both comprehensive and rigorous, combining the precision of automated tools with the nuanced insights of manual testing. The manual aspect of testing is particularly crucial, as it allows for the creation of custom-designed test cases that are directly aligned with the specific architecture and implementation details of each application. This dual approach ensures that both traditional vulnerabilities, such as SQL injection or XSS, and implementation-specific risks, are thoroughly vetted. The extensive nature of these tests ensures that no stone is left unturned in the pursuit of securing ACME’s applications.
Detailed Reporting:
Upon completing the security assessments, Blueinfy provides ACME with highly detailed reports, with zero false positives or false negatives that adhere to the firm’s stringent formatting and content requirements. These reports go beyond mere identification of vulnerabilities; they offer a comprehensive analysis that includes risk assessments, potential impact evaluations, and actionable recommendations for remediation. By delivering these insights in a clear and organized manner, Blueinfy empowers ACME’s teams to take swift and effective action, thereby reinforcing the firm’s overall security posture.
GRC Platform Integration:
To ensure that all findings are properly tracked and managed, Blueinfy seamlessly integrates the results of their security assessments into ACME’s Governance, Risk, and Compliance (GRC) platform. This integration allows for the efficient tracking of issues, timely closure of vulnerabilities, and streamlined approval processes. By embedding the findings directly into the GRC system, Blueinfy helps ACME maintain a cohesive and organized approach to risk management, ensuring that all security-related activities are thoroughly documented and easily accessible for future reference.
Management Reporting:
In addition to the technical reports, Blueinfy also provides ACME’s leadership with comprehensive management reports. These documents synthesize the outcomes of the security assessments, highlighting the unique findings identified in applications, key risk areas and offering strategic insights into the firm’s overall security posture. By presenting this high-level overview, Blueinfy enables ACME’s decision-makers to understand the broader implications of the security assessments, facilitating informed decision-making and strategic planning.
Outcome
Through its partnership with Blueinfy, ACME has achieved and maintained an exceptional security track record. After production, there have been virtually no vulnerabilities identified in annual penetration tests, production URL scans, or any other third-party assessments performed by ACME’s clients. This impeccable performance underscores the effectiveness of Blueinfy’s thorough and detailed approach to security testing. As a result, ACME continues to build and maintain trust with its clients, knowing that its applications are not only innovative but also secure, thereby reinforcing its position as a leader in the financial industry.
Article by Hemil Shah